What are Internet Connection Records, and why are they important?
As cyber crime frequency and sophistication continue to grow, Network Operators that form part of our national infrastructure are a prime target for cyber attackers seeking to cause harm. Not only that, but cyber attacks, harassment and fraud targeting individuals and Enterprises will of course traverse the Operator’s networks.
You may know about the Investigatory Powers Act. It combines powers for Police Forces, Emergency Services, and Intelligence Agencies, to acquire data (in the form of Internet Connection Records) about suspicious and harmful communications activity traversing Operator Networks, for public safety.
However, Internet Connection Records are not readily available as they were never defined in the standards for network equipment. This can be a challenge for the Network Operators who carry the UK’s communications traffic if they don’t have the means to create and supply Internet Connection Records to satisfy their regulatory obligations.
Internet Connection Records: The detail
An Internet Connection Record does not contain a copy of IP-based content, it is a file containing communications flow information, called metadata. If the collection of IP packet data can be described as an 8K dashcam recording of a road trip between London and Edinburgh (a very large video file), then metadata can be described as a small text file record of the route, journey time, and the model and registration number of the car.
There are many metadata formats. Common types include: JSON, CSV, and NetFlow. One format particularly useful for generating Internet Connection Records is a Compact Data Format set by the Internet Engineering Task Force, called IP Flow Information Export (IPFIX).
IPFIX is often seen as a content-enriched upgrade to NetFlow, as it supports nearly 500 standard elements vs NetFlow’s 100 elements. This provides the customisable means to deliver the rich metadata required to detect behavioural patterns for identifying anomalous network activity.
But as mentioned earlier, metadata needs to be generated by Network Operators, which means Internet Connection Records have to be created rather than duplicating something that readily exists in the Operator’s network.
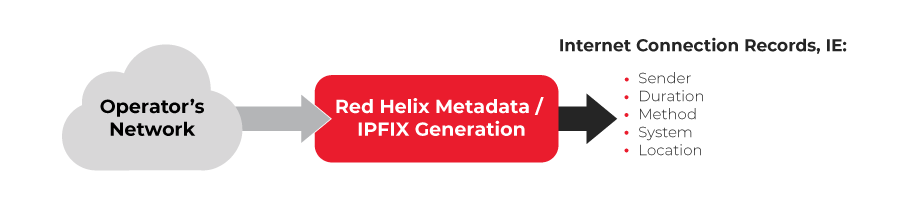
Generating IPFIX for Internet Connection Records
Using metadata generation devices enables the creation of IPFIX files enriched with the KPIs an Operator needs for satisfying Internet Connection Record needs, such as:
- The sender or recipient of a communication
- The time or duration of a communication
- The type, method or pattern, or fact, of communication
- The telecommunication system (or any part of it) from, to or through which a communication is or may be transmitted, or
- The location of any such system
The table below contains deeper detail for what might be required for Internet Connection Records, and available with IPFIX generation:
Category |
Fields |
|---|---|
| Identity | MSISDN, IMEI, CellD, IMSI if Mobile Circuit ID if Broadband |
| Flow Information | Protocol Public IP source address Public IP source port Destination IP address Destination IP port |
| Time | Start time Stop time Duration in milliseconds |
| Volumes | Packets sent / received / total Bytes sent / received / total |
| IPAR Information | Private IP address Resolved IP address TTL |
| DNS | Domain name Resolved IP address TTL |
| TLS/SSL Certificate Info | Version Hash CN Issuer Common name Server name (SNI) |
Whilst IPFIX satisfies the needs for responding to Internet Connection Record requests, it also has wider applications for Operators as they upgrade their networks and as industry regulations evolve.
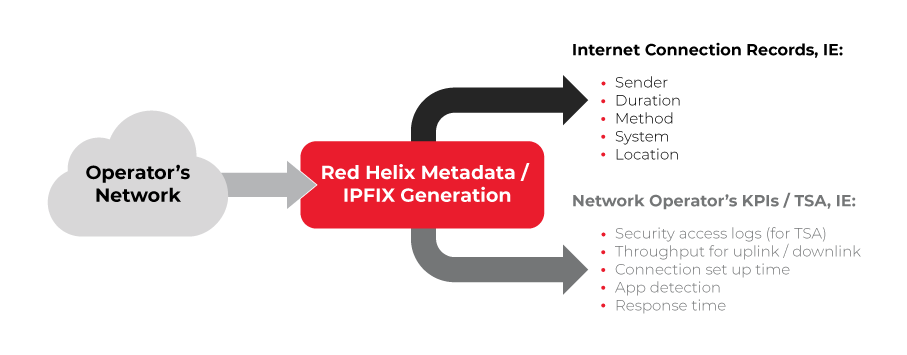
IPFIX; the ICR, TSA and network monitoring force multiplier
Regulated by Ofcom, the Telecommunications Security Act 2021 (TSA) mandates UK Network Operators to have measures in place to reduce the risk of cyber security compromises to their networks, have a plan in place to limit potential breaches, and to test their security controls.
Regulation 4 states that access logs to sensitive parts of the network and security critical functions should be recorded and made available for no fewer than 13 months, with a preference that the monitoring tools be stored in the UK.
Our tools that create unsampled IPFIX for ICRs can also generate network and security tools access log files, as illustrated in the diagram below:
This means the investments made for satisfying ICR needs can also be used for delivering part of a Network Operator’s TSA compliance, as well as its own KPIs for network performance monitoring and SLA delivery.
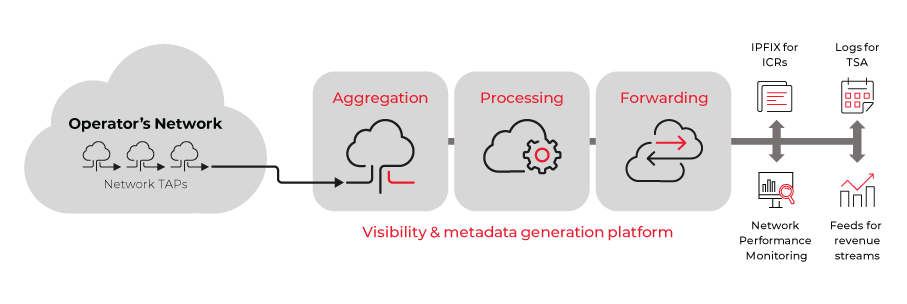
Accessing just the data you need for Internet Connection Records
Whilst tools such as ours can access data from your network, providing feeds for something specific requires the ability to prepare and deliver what’s needed. This capability is not always a given for Network Operators – as their core business is to build and maintain a high performance network.
This is where choosing a partner like Red Helix will keep you on track with the demands for accessing data from your network. We provide an intelligent blend of technology, skills and experience to various Network Operators that enables them to access just the data they need and to present it via feeds in the required speed and format.
And more recently as Operators upgrade to 5G, 400Gbps and even 800Gbps, we can enable monitoring continuity with the generation of unsampled IPFIX metadata, and other formats.
Whether you need to respond to Internet Connection Record requests, comply with TSA regulations, or generate feeds for revenue streams like location-based advertising and retail site planning, we can design, provision, and even manage a data and metadata generation platform that enables fast and thorough delivery.
Learn more about our Network Visibility services and solutions that enable this, or to discuss your data/metadata generation and cyber monitoring needs now, please contact us using the short form below.